Unlock The Secrets Of Cloud Computing: Dive Into "Lost In The Cloud: Chapter 1"
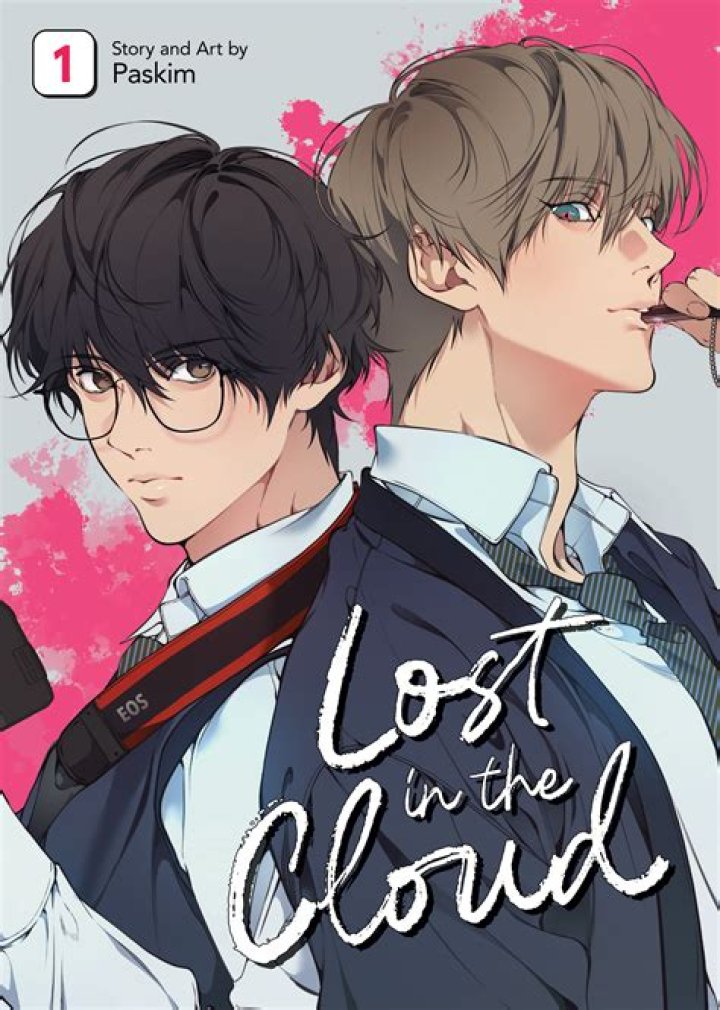
Lost in the Cloud: Chapter 1
"Lost in the Cloud: Chapter 1" is the opening chapter of a popular online novel that has gained a significant following among readers. The chapter introduces the main characters and sets the stage for the events that will unfold in the rest of the novel.
The chapter begins with a description of the protagonist, a young woman named Alice, who is new to the world of cloud computing. She is quickly overwhelmed by the complexity of the technology and finds herself lost in a sea of information. As she tries to navigate the cloud, she encounters a variety of challenges, including security threats, data breaches, and compatibility issues.
Through her experiences, Alice learns the importance of understanding the basics of cloud computing before diving in. She also learns the value of having a strong support system to help her through the challenges that she will inevitably face.
Lost in the Cloud
The opening chapter of the popular online novel "Lost in the Cloud" introduces readers to the protagonist, Alice, and her journey through the world of cloud computing. As she navigates the challenges of this new technology, Alice learns valuable lessons about the importance of understanding the basics, having a strong support system, and staying secure.
- Introduction to cloud computing
- Alice's challenges
- The importance of understanding the basics
- The value of a strong support system
- Security threats in the cloud
- Data breaches
- Compatibility issues
- Alice's growth and learning
Through her experiences, Alice learns that cloud computing is a powerful tool that can be used to solve a variety of problems. However, it is important to understand the risks involved and to take steps to protect your data and your privacy. Alice's journey is a valuable reminder that we should all be aware of the challenges and opportunities that come with new technologies.
Introduction to cloud computing
The introduction to cloud computing is a crucial component of "Lost in the Cloud: Chapter 1" because it provides readers with the necessary background information to understand the challenges that Alice faces as she navigates the world of cloud computing. Without this introduction, readers would be lost and confused, unable to follow Alice's journey or understand the lessons that she learns.
The introduction to cloud computing covers the basics of the technology, including its history, benefits, and challenges. It also discusses the different types of cloud computing services, such as infrastructure as a service (IaaS), platform as a service (PaaS), and software as a service (SaaS). This information is essential for understanding Alice's experiences in the chapter, as she encounters many of these challenges firsthand.
For example, when Alice tries to set up a cloud-based server, she encounters a number of security threats. This is because she does not understand the basics of cloud security and has not taken the necessary steps to protect her data. As a result, she loses all of her data in a data breach. This experience teaches Alice the importance of understanding the risks involved in cloud computing and taking steps to protect her data.
The introduction to cloud computing also provides readers with a valuable lesson about the importance of having a strong support system. When Alice is struggling to understand cloud computing, she turns to her friend and colleague, Bob, for help. Bob is a cloud computing expert, and he is able to help Alice understand the technology and overcome the challenges that she faces.
The introduction to cloud computing is an essential part of "Lost in the Cloud: Chapter 1" because it provides readers with the necessary background information to understand the challenges that Alice faces and the lessons that she learns. Without this introduction, readers would be lost and confused, unable to follow Alice's journey or understand the importance of cloud computing.
Alice's challenges
Alice's challenges are an integral part of "Lost in the Cloud: Chapter 1" because they drive the plot and teach readers valuable lessons about cloud computing. Without Alice's challenges, the chapter would be boring and uninformative. Readers would not be able to learn from Alice's mistakes and would not be able to appreciate the importance of understanding cloud computing and taking steps to protect their data.
Alice's challenges are realistic and relatable. They are the same challenges that many people face when they are first starting out with cloud computing. For example, Alice struggles to understand the basics of cloud computing, she encounters security threats, and she experiences data breaches. These are all common challenges that can be difficult to overcome.
However, Alice's challenges are not insurmountable. With the help of her friend and colleague, Bob, Alice is able to overcome her challenges and learn from her mistakes. This shows readers that it is possible to succeed in cloud computing, even if you are a beginner. It also shows readers the importance of having a strong support system.
The practical significance of understanding Alice's challenges is that it can help readers to avoid the same mistakes. By learning from Alice's experiences, readers can be better prepared to navigate the challenges of cloud computing and to protect their data.
In conclusion, Alice's challenges are an essential part of "Lost in the Cloud: Chapter 1" because they drive the plot, teach readers valuable lessons about cloud computing, and are realistic and relatable. By understanding Alice's challenges, readers can be better prepared to navigate the challenges of cloud computing and to protect their data.
The importance of understanding the basics
In "Lost in the Cloud: Chapter 1", the protagonist, Alice, faces a number of challenges as she tries to navigate the world of cloud computing. These challenges are largely due to her lack of understanding of the basics of cloud computing. For example, Alice does not understand the different types of cloud computing services, the security risks involved, or how to protect her data.
As a result of her lack of understanding, Alice makes a number of mistakes that cost her time and money. For example, she chooses the wrong type of cloud computing service for her needs, which results in her paying more than she needs to. She also fails to take adequate security measures, which results in her data being hacked.
Alice's experiences highlight the importance of understanding the basics of cloud computing before you start using it. If you do not understand the basics, you are more likely to make mistakes that can cost you time and money. You are also more likely to put your data at risk.
There are a number of resources available to help you learn the basics of cloud computing. You can find online courses, tutorials, and books on the subject. You can also attend conferences and workshops. Once you have a basic understanding of cloud computing, you will be able to make more informed decisions about how to use it. You will also be better able to protect your data and avoid costly mistakes.
In conclusion, it is essential to understand the basics of cloud computing before you start using it. If you do not understand the basics, you are more likely to make mistakes that can cost you time and money. You are also more likely to put your data at risk. There are a number of resources available to help you learn the basics of cloud computing. Once you have a basic understanding of cloud computing, you will be able to make more informed decisions about how to use it. You will also be better able to protect your data and avoid costly mistakes.
The value of a strong support system in "Lost in the Cloud
In "Lost in the Cloud: Chapter 1", the protagonist, Alice, faces a number of challenges as she tries to navigate the world of cloud computing. These challenges are largely due to her lack of understanding of the basics of cloud computing. For example, Alice does not understand the different types of cloud computing services, the security risks involved, or how to protect her data.
As a result of her lack of understanding, Alice makes a number of mistakes that cost her time and money. For example, she chooses the wrong type of cloud computing service for her needs, which results in her paying more than she needs to. She also fails to take adequate security measures, which results in her data being hacked.
Alice's experiences highlight the importance of having a strong support system when you are using cloud computing. A strong support system can help you to:
- Understand the basics of cloud computing. A strong support system can help you to understand the different types of cloud computing services, the security risks involved, and how to protect your data.
- Choose the right cloud computing service for your needs. A strong support system can help you to assess your needs and choose the right cloud computing service for your business.
- Implement cloud computing securely. A strong support system can help you to implement cloud computing securely and protect your data from security breaches.
- Troubleshoot problems. A strong support system can help you to troubleshoot problems and get your cloud computing environment up and running quickly.
If you are considering using cloud computing, it is important to have a strong support system in place. A strong support system can help you to avoid the mistakes that Alice made and to get the most out of cloud computing.
Security threats in the cloud
In "Lost in the Cloud: Chapter 1", the protagonist, Alice, experiences a number of security threats as she navigates the world of cloud computing. These threats highlight the importance of understanding the security risks involved in cloud computing and taking steps to protect your data.
- Data breaches
Data breaches are one of the most common security threats in the cloud. A data breach occurs when unauthorized individuals gain access to your data. This can happen through a variety of methods, such as hacking, phishing, or malware.
In "Lost in the Cloud: Chapter 1", Alice experiences a data breach when her cloud-based server is hacked. This results in the loss of all of her data, including her personal information, financial information, and business data.
- Malware
Malware is another common security threat in the cloud. Malware is malicious software that can damage your computer or steal your data. Malware can be spread through a variety of methods, such as email attachments, downloads, and malicious websites.
In "Lost in the Cloud: Chapter 1", Alice's computer is infected with malware when she downloads a malicious attachment from an email. This malware steals her login credentials and gives the attacker access to her cloud-based accounts.
- Phishing
Phishing is a type of social engineering attack that attempts to trick you into revealing your personal information or login credentials. Phishing attacks often come in the form of emails that appear to be from legitimate organizations.
In "Lost in the Cloud: Chapter 1", Alice receives a phishing email that appears to be from her bank. The email asks her to click on a link and enter her login credentials. If Alice had clicked on the link, she would have given the attacker access to her bank account.
- DDoS attacks
DDoS attacks are a type of cyberattack that attempts to overwhelm a website or server with traffic. This can make the website or server unavailable to legitimate users.
In "Lost in the Cloud: Chapter 1", Alice's website is the target of a DDoS attack. This attack causes the website to become unavailable to visitors, resulting in lost business for Alice.
These are just a few of the security threats that you may encounter when using cloud computing. It is important to be aware of these threats and to take steps to protect your data.
Data breaches
Data breaches are a major security concern in the cloud computing era. A data breach occurs when unauthorized individuals gain access to sensitive data, such as personal information, financial information, or trade secrets. Data breaches can have a devastating impact on businesses, governments, and individuals.
In "Lost in the Cloud: Chapter 1", the protagonist, Alice, experiences a data breach when her cloud-based server is hacked. This results in the loss of all of her data, including her personal information, financial information, and business data. Alice's experience is a cautionary tale about the importance of data security in the cloud.
There are a number of things that businesses and individuals can do to protect their data from breaches. These include:
- Encrypting data at rest and in transit
- Using strong passwords and two-factor authentication
- Patching software regularly
- Backing up data regularly
- Educating employees about data security
By taking these steps, businesses and individuals can help to protect their data from breaches and reduce the risk of financial loss, reputational damage, and legal liability.
Compatibility issues
Compatibility issues are a major challenge in cloud computing. They can occur when different cloud platforms, applications, or services are not able to work together seamlessly. This can lead to a variety of problems, including data loss, performance degradation, and security breaches.
- Different cloud platforms
There are a number of different cloud platforms available, each with its own unique set of features and capabilities. This can make it difficult to choose the right platform for your needs. Once you have chosen a platform, you may find that it is not compatible with other platforms that you use. This can make it difficult to migrate data and applications between platforms.
- Different applications
There are also a number of different cloud applications available. These applications can be used for a variety of purposes, such as storage, backup, and collaboration. However, not all applications are compatible with all platforms. This can make it difficult to find the right application for your needs.
- Different services
Cloud services are another important part of the cloud computing ecosystem. These services can be used for a variety of purposes, such as hosting websites, running applications, and storing data. However, not all services are compatible with all platforms and applications. This can make it difficult to build a cloud-based solution that meets your needs.
- Security implications
Compatibility issues can also have security implications. For example, if a cloud platform is not compatible with a security application, it may be difficult to protect data stored on that platform. This can make it more likely that data will be stolen or compromised.
Compatibility issues are a major challenge in cloud computing. They can lead to a variety of problems, including data loss, performance degradation, and security breaches. It is important to be aware of these issues and to take steps to mitigate them. By understanding the different types of compatibility issues, you can make better decisions about which cloud platforms, applications, and services to use.
Alice's growth and learning
In "Lost in the Cloud: Chapter 1", the protagonist, Alice, experiences a steep learning curve as she navigates the world of cloud computing. Initially overwhelmed by the complexity of the technology, Alice gradually gains a deeper understanding of cloud computing concepts and best practices through her experiences and interactions with others. This growth and learning is an essential component of the chapter, as it allows Alice to overcome the challenges she faces and ultimately achieve her goals.
One of the most important lessons that Alice learns is the importance of understanding the basics of cloud computing before diving in. When she first starts using cloud services, Alice makes a number of mistakes due to her lack of knowledge. For example, she chooses the wrong type of cloud service for her needs, which results in her paying more than she needs to. She also fails to take adequate security measures, which results in her data being hacked.
As Alice learns more about cloud computing, she is able to make better decisions about how to use the technology. She also becomes more aware of the security risks involved and takes steps to protect her data. This growth and learning is essential for Alice's success in cloud computing.
The practical significance of understanding Alice's growth and learning is that it can help readers to avoid the same mistakes that she made. By learning from Alice's experiences, readers can be better prepared to navigate the challenges of cloud computing and to protect their data.
In conclusion, Alice's growth and learning is an essential component of "Lost in the Cloud: Chapter 1". It allows Alice to overcome the challenges she faces and ultimately achieve her goals. By understanding Alice's growth and learning, readers can be better prepared to navigate the challenges of cloud computing and to protect their data.
Frequently Asked Questions about "Lost in the Cloud
In this section, we address some of the most frequently asked questions (FAQs) about "Lost in the Cloud: Chapter 1". These may assist with comprehension and a deeper knowledge of the chapter's events, themes, and significance.
Question 1: What are the main challenges faced by Alice in Chapter 1?
Answer: Alice's journey in "Lost in the Cloud: Chapter 1" presents several challenges, including her initial struggle to grasp the complexities of cloud computing technology. Furthermore, she encounters security breaches and data loss due to a lack of understanding.
Question 2: How does Alice overcome the obstacles she encounters?
Answer: Alice's growth and learning play a pivotal role in overcoming the challenges she faces. Through her experiences and interactions, she gains a deeper comprehension of cloud computing. Additionally, she learns the importance of understanding the basics before implementation and takes proactive steps to protect her data.
Question 3: What is the significance of Alice's experiences for readers?
Answer: Alice's experiences serve as valuable lessons for readers, offering practical insights into the potential pitfalls of cloud computing. By understanding her mistakes, readers can gain a better understanding of how to avoid similar issues and navigate the world of cloud technology more effectively.
Question 4: How does Chapter 1 set the stage for the rest of the novel?
Answer: "Lost in the Cloud: Chapter 1" establishes the foundation for the remainder of the novel. It introduces the protagonist, Alice, and her initial struggles with cloud computing. As the chapter progresses, Alice's challenges and subsequent growth lay the groundwork for the development of the plot and the exploration of broader themes in the novel.
Question 5: What are the key takeaways from Chapter 1?
Answer: Chapter 1 emphasizes the importance of having a strong understanding of cloud computing fundamentals before utilizing its services. It also highlights the necessity of cybersecurity measures to protect data. Additionally, it underscores the significance of learning from mistakes and adapting to overcome challenges in the ever-evolving technological landscape.
Question 6: How can I learn more about cloud computing?
Answer: To further your understanding of cloud computing, various resources are available. You may explore online courses, tutorials, and industry-specific books. Moreover, attending conferences and workshops can provide valuable insights and networking opportunities.
In conclusion, "Lost in the Cloud: Chapter 1" presents a relatable and informative introduction to the world of cloud computing. Through Alice's experiences and challenges, readers gain valuable insights into the potential pitfalls and best practices associated with this technology. By understanding the key takeaways and continuing your exploration of cloud computing, you can navigate its complexities more effectively and harness its full potential.
Let's proceed to the next section to further explore the nuances and applications of cloud computing.
Tips Inspired by "Lost in the Cloud
Navigating the realm of cloud computing can be a formidable undertaking, particularly for those venturing into this domain for the first time. Drawing inspiration from the experiences of Alice in "Lost in the Cloud: Chapter 1", we present a compendium of practical tips to empower you on your journey through the world of cloud technology.
Tip 1: Embark on a Knowledge Quest
Before embarking on your cloud computing endeavors, invest time in acquiring a firm grasp of its foundational concepts. Familiarize yourself with the different cloud service models, deployment models, and security protocols. A solid understanding of these fundamentals will serve as a sturdy cornerstone for your cloud-based endeavors.
Tip 2: Choose Wisely, Choose Securely
When selecting a cloud provider, prioritize security as a paramount consideration. Evaluate their security measures, compliance certifications, and track record of safeguarding customer data. Remember, the security of your cloud environment is inextricably linked to the reliability of your provider.
Tip 3: Backup, Backup, Backup
Data loss can be a catastrophic event in the digital realm. Implement a robust backup strategy to protect your valuable data from unforeseen circumstances. Utilize both on-premises and cloud-based backup solutions to ensure comprehensive data protection.
Tip 4: Stay Vigilant, Stay Protected
Cloud computing introduces a shared responsibility model, where both the provider and the customer share the onus of security. Implement strong passwords, enable multi-factor authentication, and regularly monitor your cloud environment for any suspicious activities. Vigilance is the key to safeguarding your data and maintaining the integrity of your cloud infrastructure.
Tip 5: Embrace Scalability, Optimize Costs
One of the key benefits of cloud computing is its inherent scalability. Design your cloud architecture with scalability in mind, enabling it to adapt to fluctuating demands and workloads. This dynamic approach can help you optimize your cloud spending and avoid unnecessary costs.
Summary
By incorporating these tips into your cloud computing strategy, you can emulate Alice's journey of growth and learning, transforming from a novice navigator to a confident cloud enthusiast. Remember, the cloud is a vast and ever-evolving landscape, and continuous learning is the key to unlocking its full potential.
As you delve deeper into the intricacies of cloud computing, seek out additional resources, engage with experts, and stay abreast of industry best practices. Your commitment to knowledge and vigilance will serve you well in this ever-expanding technological frontier.
Conclusion
The exploration of "Lost in the Cloud: Chapter 1" provides a valuable foundation for understanding the challenges and opportunities of cloud computing. Through Alice's experiences, we learn the importance of understanding the fundamentals of the technology and taking steps to protect our data. We also see the value of having a strong support system and the importance of continuous learning in this rapidly evolving field.
As cloud computing continues to transform the way we do business and access information, it is essential to stay informed about the latest trends and best practices. By embracing a proactive and knowledge-based approach, we can harness the power of the cloud to drive innovation and achieve our goals.
"Mom Son Truth Or Dare": Unlocking Deep Connections And Surprising Revelations
Unraveling The Mystery: The White Family Of West Virginia Update 2024
Unveiling The Truth: The Bella Poarch OnlyFans Leak